
Seamless Tableau SSO Integration in Web Applications
The Challenge We Faced
When our team at Ellocent Labs started building an analytics platform for one of our clients, we hit a wall that many product teams know all too well. They wanted private Tableau dashboards embedded seamlessly into their application, but every traditional SSO solution we looked at had the same annoying problem—users kept getting redirected to external login screens.
You know the drill: Microsoft login pages, Google sign-in popups, Okta screens. Sure, they're secure, but they completely break the flow of your application. One minute your user is in your beautifully designed interface, the next they're staring at a generic Microsoft blue screen.
For our client's product vision, this just wasn't going to cut it.
What We Actually Needed
After several brainstorming sessions with our engineering team at Ellocent Labs, we laid out our must-haves:
This article walks through how we actually pulled this off using Auth0—but not in the way most people use it.
Why We Ditched Traditional SSO
Here's the thing about standard SSO implementations: they're built around redirects. The whole architecture assumes users are okay with bouncing between different login screens. And maybe that works fine for internal tools where everyone's used to it.
But for a customer-facing product? It's a UX disaster.
Every time a user hits one of those redirect flows:
Our Ellocent Labs team decided to flip the script entirely. Instead of letting Auth0 control the authentication UI, we'd use it purely as an identity verification engine running quietly in the background. Everything the user sees and interacts with? That stays in our control.
Our Solution Architecture
We built something that might seem counterintuitive at first—Auth0 is there, it's verifying identities, but it's completely invisible to end users. All the orchestration happens server-side.
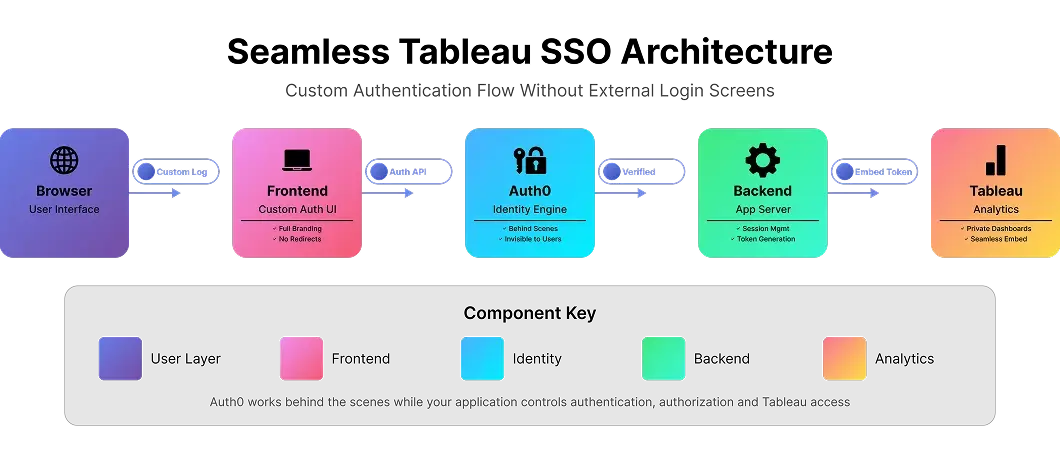
Let me walk you through how the pieces actually fit together.
How We Built It (The Real Implementation)
STEP 1
Taking Control of the Login UI
What this gave us:
When someone logs in, our frontend sends their credentials to our backend API. The backend then talks to Auth0 programmatically to verify those credentials. From the user's perspective, they're just logging into the application—nothing more, nothing less.
STEP 2
Managing Sessions Our Way
Here's where it gets interesting: those Auth0 tokens? We don't pass them around, we don't store them in the frontend, we don't send them to Tableau. They exist for about two seconds on our backend just to verify identity, then they're gone.
Instead, we maintain our own session management where we:
This separation turned out to be crucial for security. Auth0 handles the "is this person who they say they are?" question. Everything else—the "what can they do?" part—that on us.
STEP 3
The Tableau Integration Piece
Our solution: server-to-server authentication with Tableau. Essentially, Tableau trusts our backend, and our backend vouches for users.
We ended up implementing this using Tableau Connected Apps (JWT-based approach). Other teams might use Trusted Authentication or REST API tokens depending on their setup—all of these work on the same principle.
The key insight: Tableau never talks directly to the end user. It only talks to our backend, which acts as a trusted middleman.
STEP 4
Embedding Dashboards Securely
On the backend (our server):
On the frontend (user's browser):
The result: Users click on a dashboard link and it just... loads. No prompts, no waiting, no authentication friction. Just works.
Security Was Our Top Priority
Look, we're not going to pretend security was an afterthought we bolted on later. From day one at Ellocent Labs, we knew this architecture had to be bulletproof. Here's how we locked it down:
What This Actually Achieved for Us
After rolling this out, the difference was night and day:
When You Probably Shouldn't Do This
Real talk: this approach isn't right for every situation. We've seen cases where traditional SSO makes more sense:
In those scenarios, the benefits of federated identity outweigh the UX limitations we were trying to solve.
Key Lessons from Building This
After implementing this architecture at Ellocent Labs, here's what really matters:
Things to Consider Before Building This
If you're thinking about implementing something similar, here are some real considerations from our experience:
Wrapping Up
When we started this project at Ellocent Labs, we knew there had to be a better way than forcing users through external login screens. What we ended up building proved that you really can have both great security and great user experience.
The architecture we created feels invisible to users, stays completely under our control, and maintains enterprise-grade security standards. That's exactly what embedded analytics should be—a seamless part of your application, not something bolted on that feels like a separate tool.
By rethinking how we use Auth0 and integrate with Tableau, we eliminated the false choice between security and user experience. And honestly, that's made all the difference for our clients.
Schedule a 15-Minutes call
Let’s make things happen and take the first step toward success!
Got Ideas? We’ve Got The Skills.
Let’s Team Up!
Let’s Team Up!
What Happens Next?
We review your request, contact you, and sign an NDA for confidentiality.
We analyze your needs and create a project proposal with scope, team, time, and cost details.
We schedule a meeting to discuss the offer and finalize the details.
The contract is signed, and we start working on your project immediately.